Overview of Private Link:
A Private Endpoint is a special network interface (NIC) for your Azure Web App in a Subnet in your Virtual Network (VNet). The Private Endpoint is assigned an IP Address from the IP address range of your VNet. The connection between the Private Endpoint and the Web App uses a secure Private Link.
Private Link enables you to host your apps on an address in your Azure Virtual Network (VNet) rather than on a shared public address. It provides secure connectivity between clients on your private network and your Web App. By moving the endpoint for your app into your VNet you can:
1. Isolate your apps from the internet: Configuring a Private Endpoint with your app, you can securely host line-of-business applications and other intranet applications.
2. Prevent data exfiltration: Since the Private Endpoint only goes to one app, you don’t need to worry about data exfiltration situations.
Referemce: https://docs.microsoft.com/en-us/azure/app-service/networking/private-endpoint
If you just need a secure connection between your VNet and your Web App, this is the simplest solution. If you also need to reach the web app from on-premises through an Azure Gateway, a regionally peered VNet, or a globally peered VNet, Private Endpoint is the solution.
Private Link vs App Service Environment: The difference between using Private Endpoint and an ILB ASE is that ASE can host many apps behind one VNet address while Private Endpoint can have only one app behind one address.
To access your Sitecore instances (CD or CM roles) in your VNet was previously possible via ILB App Service Environment or Azure Application Gateway with an internal inbound address. In this article, we will create Private Endpoint & isolate Sitecore environment from the Internet.
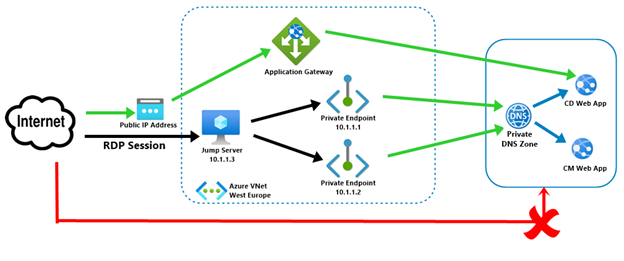
Once we will implement the above architecture, then:
1. Sitecore CD & CM web app’s public access will be disabled.
2. User can access CD instance via Application gateway public IP address. User needs to map his domain name with Application gateway.
3. To access CM instance, users need to use RDP session via Jump Server.
Follow the below steps to configure Azure Private Link for Sitecore web instances:
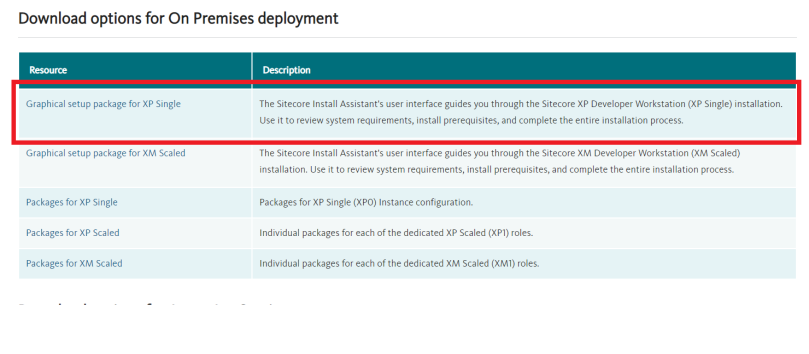
1. Go to CD instance’s App service plan & change the plan to P1v2. Currently, Private endpoint is only available in PremiumV2 plans.
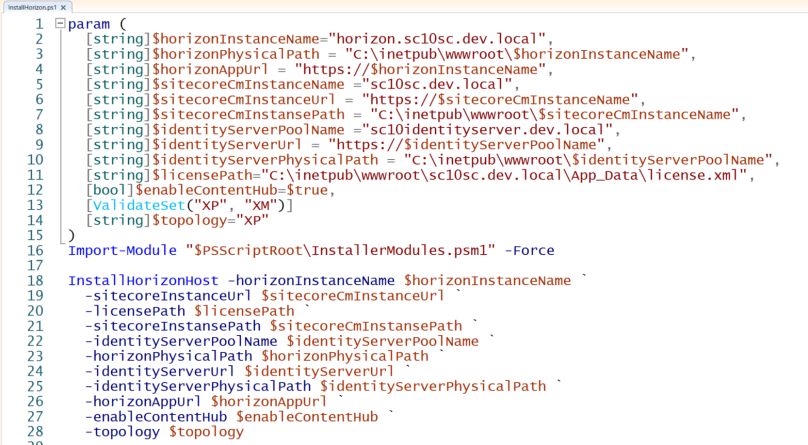
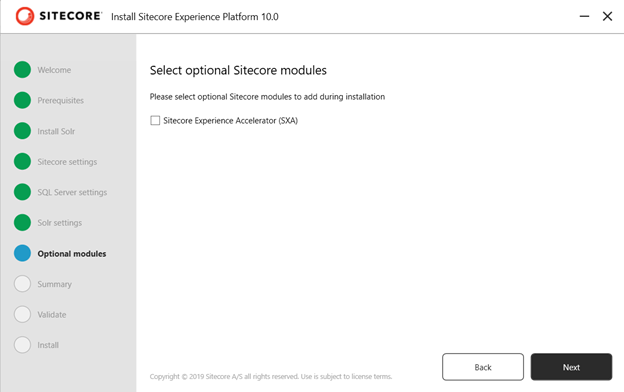
2. Create Private Endpoint. Select your Subscription & Resource Group and then enter Endpoint name & select your location as shown below.
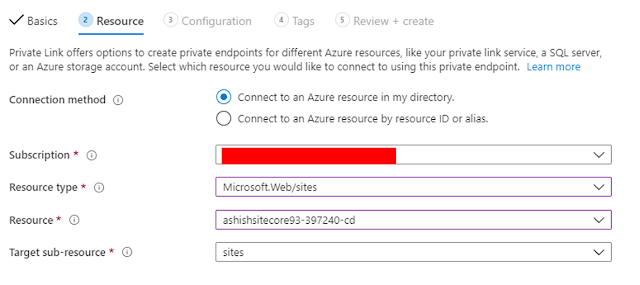
3. In Resource type, select Microsoft.Web/sites and then select your CD instance.
4. I already have Virtual Network, hence I have selected the existing virtual network. Then configure your Private DNS integration as illustrated below.


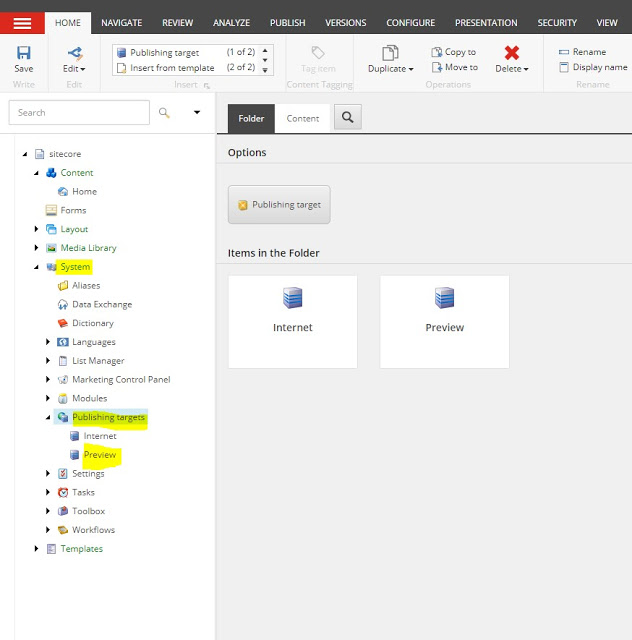
5. Perform the above steps (1-4) for CM instance.
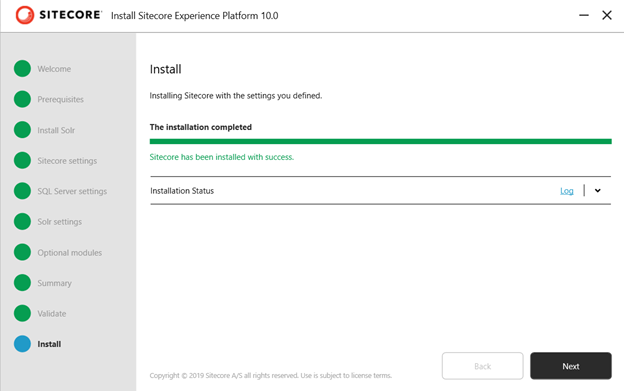
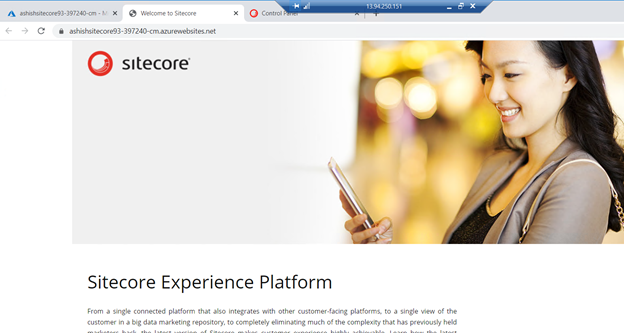
6. Open your CD & CM instance in your browser. Now you will be unable to access CD & CM instances.

7. Create a virtual machine in same Virtual Network. Open the RDP port so that this VM can act as Jump Server.
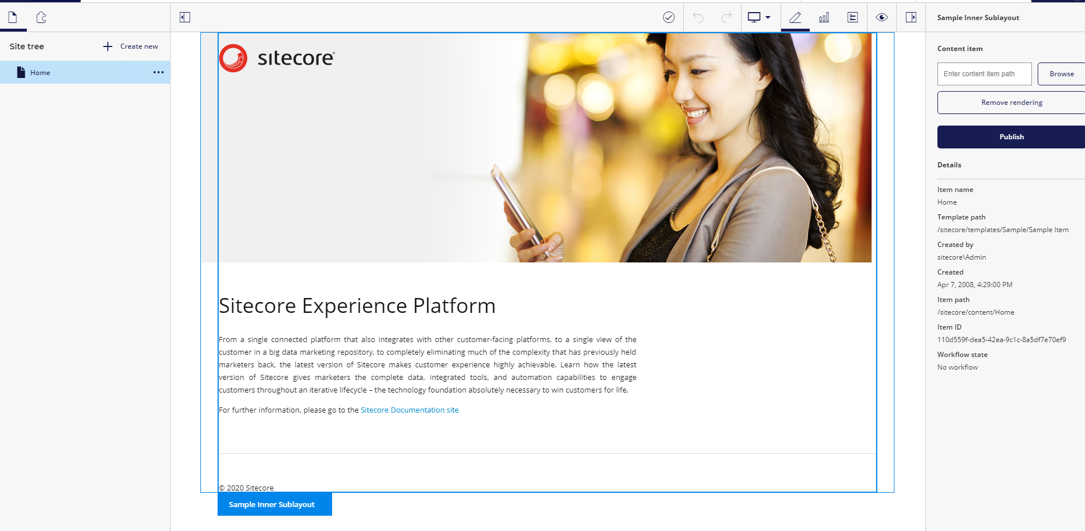
8. Once VM will be deployed, create a RDP session and browse your CD & CM instance. You should be able to access both CD & CM instances.
9. To access CD instance publicly, create an Azure Application Gateway.
9.1. Select the same Virtual Network that you have selected in above steps.
9.2. Create new Public IP address
9.3. In backend pool, select your CD instance.

9.4. Add routing rule. Create a listener and upload HTTPs certificate as shown below.

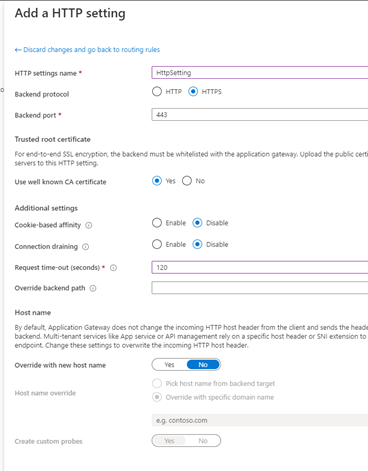
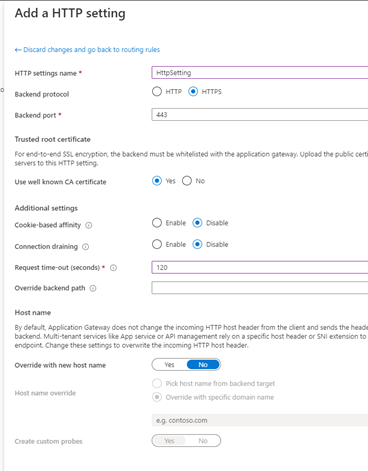
Create HTTP setting as illustrated below.
9.5. Once Application gateway will be deployed, check your backend health.

10. Navigate Application Gateway’s IP address in browser. You will be able to access CD instance publicly and your instance is secured by Private IP & your requests go through a Virtual Network.
I hope this information helped you. If you have any feedback, questions or suggestions for improvement please let me know in the comments section.